# Side channel attacks
Thomas De Cnudde <thomas.decnudde@student.kuleuven.be>
**software is a list of sequential instructions!**
done! that was a good block.
pin code checking software: check if the user entered the right pin code
software runs on "something"; in this case "hardware"
"it ultimately instructs hardware to operate"
```
user
----------
application software
-----------
operating system
-----------
hardware
```
layers!
"leakage from boundaries" is what is considered side channel attacks
dilation of the pupil will tell what you are calculating! very innocent
extra information = side channel = revealed information
unintentionally, unaware of it, not clear the mechanics behind
pupil as 'side channel' from the brain
pupils leak information
follows laws we might never discover (mechanics of the human body)
a software running on a hardware
it emanates radio-magnetic waves, acting like an antenna (fracking)
you can build an antenna and use it to capture the waves and reconstruct what the user is doing
electromagnetic radiation gives information on your devices
once you are aware of it, it is hard to control but can be mitigated: put it in a cage made of metal
mitigate
why look at this problem?
bad people want to steal your money
or they want to side channel your hardware to retrieve the way your algorithm works, break intellectual property
what can they steal?
they can steal values but also intellectual property
"hardware lives in the real world and real world properties lead to side channels"
"side channel attacks exist because we live in a real world"
"real world properties lead to side changels" (= angels of change? ) :)
properties:
* computation speed
* area
* power consumption
* reliability
some side channels
* timing
* power consumption
* electromagnatic radiation
* light, sound, temperature (exotic)
algorithms as a target
(patents, intellectual property)
we enter 4 random numbers
* algorithm checks it
* if it is wrong it stops
* if first digit is right, it proceeds to check the second digit etc.
* with timing analysis, we can see already if the first digit is wrong, if the program checks the first digit first
you can divide
and conquer! :P
power analysis / electromagnetic analysis is simple : one or two measurements
* duration - how long an operation takes before it goes silent (power gives information on timing)
* amplitude
ATCPOTW: All the computation power of the world
just by measuring the power consumption you can retrieve information
what to do against it?
* shielding
* confusing by noise
how do you derive the key from this power analysis?
looking at the algorithm itself?
ex = in public key cryptography,
rsa is computed by a squaring operation (x^2) or multiplication
squaring is optimized, results as green in an analysis of power consumption
multiplication instead is not, so results red (more consumption) in the graph
green computation takes less time and power than the red computation
these are optimized for speed and your battery
x^2 is green and x.y is red
the algorithm dictates which function you use
a key: 100101
is basically such that
all ones are green
and all zeros are red
(or the other way around)
a counter-measure is to add red power consumption like patterns after the red power consumption units.

![]http://etherbox.local/home/pi/images/thursday/138873.jpg)
template attacks (wah)
you can create templates if you have control over a device
where you can build curves that represent the different values that are being executed
preferably have the same device as one you want to attack
the best is from the same fabrication, but this is not necessary
what is necessary is to have the same mechanisms for drawing on power
Kym: what about retro-active mimesis
in ww2, having access to the enigma, they could replicate the encryption type
enigma on the mathematical side of crypto, here we are in the electrical side of crypto
"enigma was an algorithm"
enigma provided the algorithm
without the algorithm you know nothing and cannot get the keys
in ww2, navajo language was used
you cannot break the cipher without knowing that it is that language
(it was more difficult for nazis to find native speakers of navajo)
_Philip Johnston, a civil engineer for the city of Los Angeles,[13] proposed the use of Navajo to the United States Marine Corps at the beginning of World War II. Johnston, a World War I veteran, was raised on the Navajo reservation as the son of a missionary to the Navajo. He was one of the few non-Navajo who spoke the language fluently. <https://en.wikipedia.org/wiki/Code_talker#Navajo_code_talkers>_
for the US army it was difficult, too. ;) .. Good appropriation of the language of an oppressed minority for military use.
when you do certain manipulations on your machine
it uses energy in pulses
you are listening to the pulses
you recreate the content of another machine
in WWII, they got one of the machines
they then knew how the machine worked
they didn't know the presets necessary to break enigma
they used the weather reports: they always started with heil hitler
that was the key
they first got the algorithm by getting the machine
they still needed to retrieve the key that changed everyday
the first recorded side channel attack was on a mechanical device by placing microphone in the office and recording the device's clicks in order to break the code
a lot of side-chan come from engineers trying to optimize things
side-channel comes from technology we use
CMOS technology
a lot of gates that can be either closed or open
the transition from open to closed requires effort, consumes power and makes sound
high pitch sounds => + electromagnetic field
& heat from friction
attackers are "passive" in that they only observe -> no interaction
actually you can observe if you are being observed, hence once again no detached observation
passive and non invasive attacker
models of attackers
passive and non-invasive attackers
cost of attack: 300 euros
adversaries: only allowed to observe but not allowed to interact (Read 444)
(how do you design a system that notices when it is observed? <- VW case :) that's when you know _how_ you will be observed. who is observing who in the VW case?)
**engineers are good guys!**
how can you think about the ways bad people will use the technology
how does this software circulate? there are software suites
chip whisperer - also a friendly guy, canadian
<https://wiki.newae.com/Main_Page>
(no animal mascotte? but FLOSS ... :P )
not sure if it is legal
(they make their own stuff) brilliant guys
fault attacks are more powerful but more expensive
## counter-measures and prevention
"if we keep computing we need counter-measures"
OS - restrict certain things system can do
software layer - how will users use the system - how will the adversary misuse the system
= changing the approach : from how will the user will use it to how will it be misused
how to design to prevent side channel analysis?
shift from observing a potential user to being observed by a potential adversary
software
classic system designers
how will the user use the system
new designers
how will the adversary misuse the system?
problem: can you ever know all attacks?
countermeasures are tailored to what we know
preventing side-channel analysis (when is it analysis and when is it attack?)
try to eliminate side channels
noise generators
balancing power consumption
insert dummy operation => timing purposes (make software "time independent" which means making the run-time non correlative to the o
in order to make all operations having same length (leaking useles infos)
```
- V V V V
- <------->
- X D D D
```
drains your battery
heightens your ecological footprint
## methods for preventing side-channel analysis
* Make Software Time Independent: insert dummy operations (could these be deployed for aesthetic or other purposes instead of being purely dummy operations?)
* Randomizing Data - masking
* Randomizing Operation Order - shuffling, random delays (like when preventing theft: making measures to delay the intruder)
* Shielding - a Faraday cage
* Logic Styles
differential power analysis
question of how to isolate an algorithm when another process is occurring
different attacker models
* one has device in advance and can manipulate it
* the other only can observe from a distance without prior knowledge
try to extract a model in order to make widely applicable counter measures
masking
boolean masking <https://perso.uclouvain.be/fstandae/PUBLIS/49.pdf>
reconstruction
power analysis is probing
if you have one probe, you can never fully retrieve the original value
one observation reveals no information (probing model)
with two observations you are able to remove one source of masking
using 2 random values breaks masking (...)
design new systems considering the new requirements:
area, speed, power (old model)
there is also an interest in considering security
Intel SGX: <https://software.intel.com/en-us/blogs/2013/09/26/protecting-application-secrets-with-intel-sgx>
if you design software, you need to consider the hardware because hardware is the link between software and the real world
push security down to low levels
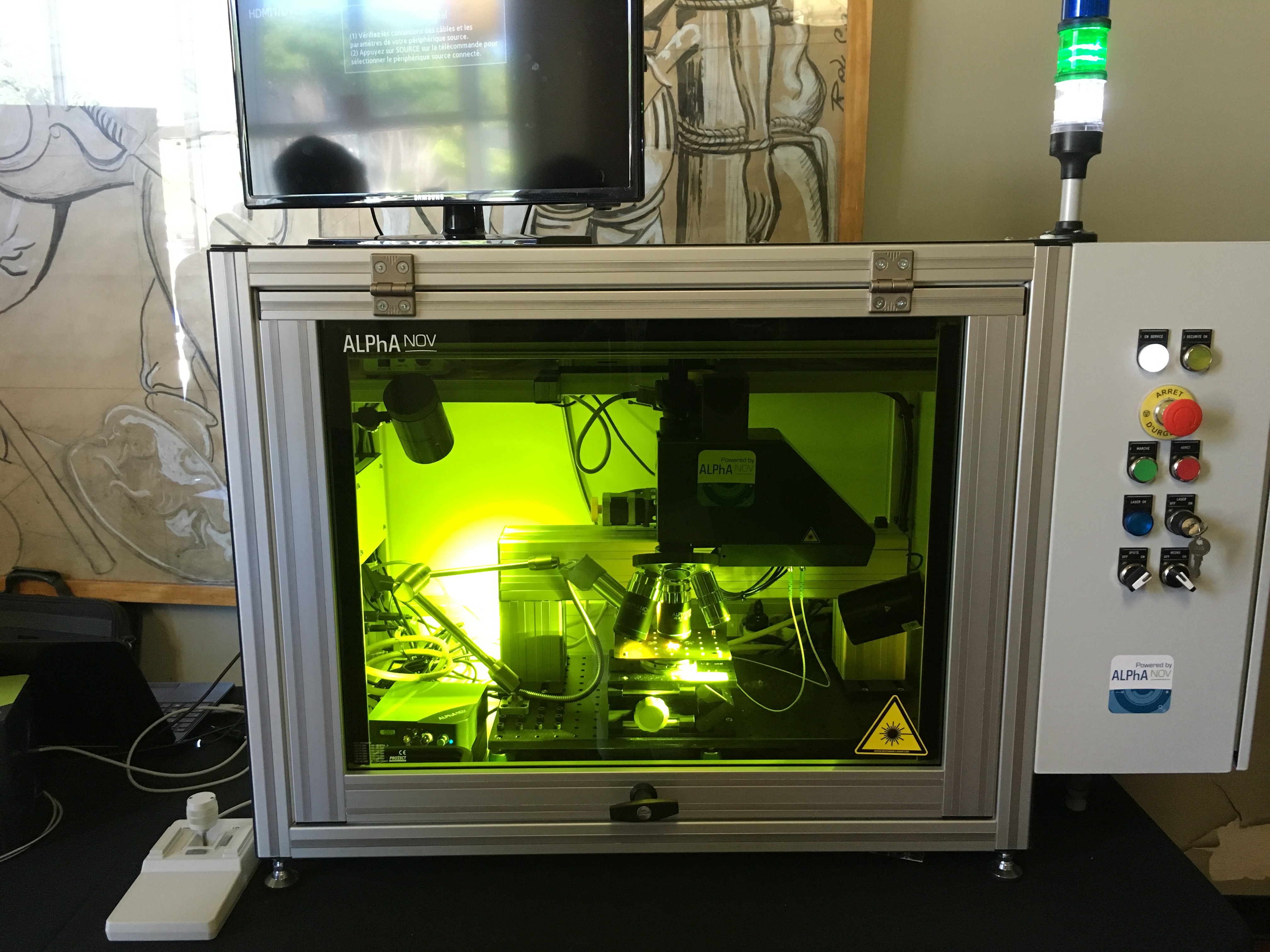
fault injections (laser)
<http://cryptologie.net/home/all/3>
full architectural reports of chips!
<https://www.texplained-store.com/en/5-architectural-reports>
full scans of chips, so to know where to use the laser on, etc. (on SALE now!!)
<https://www.texplained-store.com/en/3-images>
let's buy some!
is software and hardware the same thing?
does the observation of software and hardware are distinct?
VHDL: hardware description language
xilinx design language - description file/configureation file in human readable form of native CIRCUIT description -> gets compiled - bitstream generator -> takes the machine version and configures trough 0s 1s the wires -> the gates
so a data/descriptor file -> compiler -> circuit
"Hardware for me is made of silicon, software a sequence of bits in a file. But naturally I am biased: I'm a hardware desginer so I like to consider it as unique and special".
"We are observing software through the hardware" ultimately starts and end with software
you have the algorithm and the device
break the hardware by running some known software on it and the record a profile to build a model that then reveals the hardware (example of using software to break hardware)
and in other contexts you can break the software using hardware
"I totally forgot about punchcards"
computers as people
"my (m)other was a computer" [^mother]
<https://library.memoryoftheworld.org/b/x1Ectf3ojxJTcaop8ivmZs1eeku8yYCz0bjnPgBItRmSlZuD>
(sidenote: in dutch: 'rekenmeisje' of 'rekenaarster' = calculation girl / woman = fr: calculatrice)
searching for patterns? What is an electrical trace / recording of the operation of software on hardware?
FPGA (field programmable gate array) = huge array of switches / user can program which gates are active > generate a hardware description using code (VHDL/ verilog)
<https://en.wikipedia.org/wiki/Field-programmable_gate_array>
programmable integrated circuit
tons of gates
reconfigurable computing is interesting for counter measures
back to hardware programming
parallelism and reducing (low level) variability
"the mapping is not deterministic"
last question: what are your tools?
* m(e/a)thlab, toolbox
* matlab
* oscilloscopes (very cool ones)
* em probes (antennas) which let you localize measurements
first ones to do side channel analysis were biologists, using old Tektronix oscilloscope with phosphorus screen, had to work at night to observe the peaks
electromagnetic probes to look for where the encryption is
<http://www.tek.com/support/faqs/tektronix-near-field-probe-kit-tektronix-p-n-119-4146-00>
<http://gizmodo.com/why-mathematicians-are-hoarding-this-special-type-of-ja-1711008881>
Paul Kosher -> bio engineers doing side channel attacks
F: 'software-curious' people
[^mother]: From the introduction to My Mother was a computer: _In Neal Stephenson’s Cryptonomicon, the fictional mathematical genius Lawrence Pritchard Waterhouse is showing off his new mechanical invention to his supervisor, Lieutenant Colonel Earl Comstock. Comstock inquires: “If you had to give a name to the whole apparatus, what would you call it?” “Hmmm,” Waterhouse says. “Well, its basic job is to perform mathematical calculations—like a computer.” Comstock snorts, “A computer is a human being.”_
(...)
The semantic shock the sentence is likely to give us today is rooted not only in the shift from human to machine labor, but also in the feeling that a kinship category essential to human society has been violated.